
“There is a way out of every box, a solution to every puzzle; it's just a matter of finding it.”
- Captain Jean-Luc Picard (Episode 160, Star Trek: The Next Generation)
Traditional security solutions protect sensitive data at ingress and egress - by preventing unauthorized access and by defending against loss and exfiltration. That’s only part of the challenge. Value and insights are derived from data when in use, and data-in-use leads to complexities and increased vulnerabilities. In reality, most solutions don’t address the big black box of vulnerability that access control and DLP aren’t designed to address.
Our focus at Dasera is breaking open the black box & solving the data security puzzle, by ensuring that the entire data lifecycle - from creation to deletion - is secure. 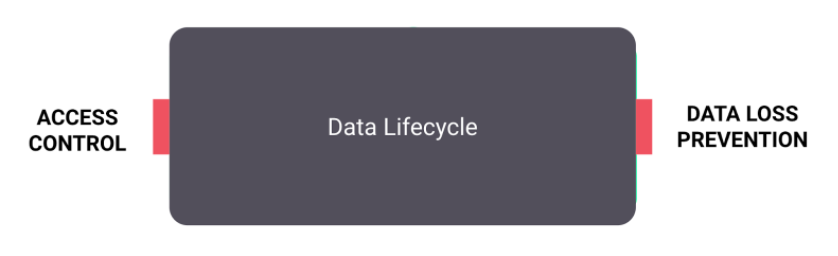 Recently, I discussed the challenges of cloud data security with SANS Instructor and practicing attorney, Benjamin Wright. During the live webinar, I shared technical use cases and solutions for a variety of customer challenges including how to “Prevent Your Data From Going Rogue” by:
Recently, I discussed the challenges of cloud data security with SANS Instructor and practicing attorney, Benjamin Wright. During the live webinar, I shared technical use cases and solutions for a variety of customer challenges including how to “Prevent Your Data From Going Rogue” by:
- Discovering and securing sensitive data across thousands of cloud data stores
- Classifying sensitive data and protecting it with granular policies that align to your business context
- Detecting data misuse in cloud data warehouses as well as production databases without impacting database performance
We interacted with the audience through polls and real-time chat to share our industry-crossing perspectives, and I challenged them to consider these questions:
- In a cloud-first world where data stores can be created by a single click, do you always know “Where is your data?”
- Are your data stores backed-up? encrypted? publicly accessible? “Are your data stores securely configured?” All. The. Time.
- With per table/per schema policies for sharing, as well as ease of copy, export, joins, do you know “Where is all of your sensitive data?”
- Are individual permissions consistent across your cloud infrastructure with permissions in line with changing roles & responsibilities? “Is access control following least-privileged and uniform?”
- Data use generates value, but “Is data usage creating privacy & exfiltration risks?”
- The ease of data capture and accessibility in the cloud can lead to data sprawl and create challenges for archival and deletion when it’s critical to know “Where is every copy of my data?
Which of these questions most resonates with you? Do more than a few give you reason to pause? If so, I invite you to watch the replay and join the conversation with us on Twitter & LinkedIn as we continue to tackle and solve your data lifecycle challenges.
Onwards and upwards,
April
Learn more at www.dasera.com









