
Hello earthlings, look out from your windows. Winter's gone. It's spring!

As you jumped from one web conference call to another and the world adjusted to a new normal, we did a quick media reconnaissance. The intent - to summarize all that's going on in the world of cybersecurity and insider threats.
We'd be remiss if we did not begin with a quick and respectful nod to the COVID-19 pandemic. Through the last couple of months, it has burned the workplace to a crisp and opened up an Alaska-sized wormhole of cybersecurity issues in almost every corner of the world.
Trolls had a field day with Zoom-bombing. It started out as pranks and jokes, but soon spiraled into potential cybersecurity concerns for firms. Add to that good-old phishing emails and malware.
End result - security teams are on overdrive. Hang in there, dear friends. And enjoy this news summary we put together for you.
You Had me at Trust

With most employees working remotely from their own networks, some even on their devices, the line between insider and outsider has blurred. This made our second re-read of Ponemon Institute's The Cost of Insider Threats 2020 an even wilder ride. In case you missed it:
- Over the last two years, the number of incidents increased by 47%.
- Out of all the attacks, 191 were related to the theft of users’ credentials.
- It takes an average of 77 days to contain an insider incident.
- The overall cost of the average insider breach is >$11M.
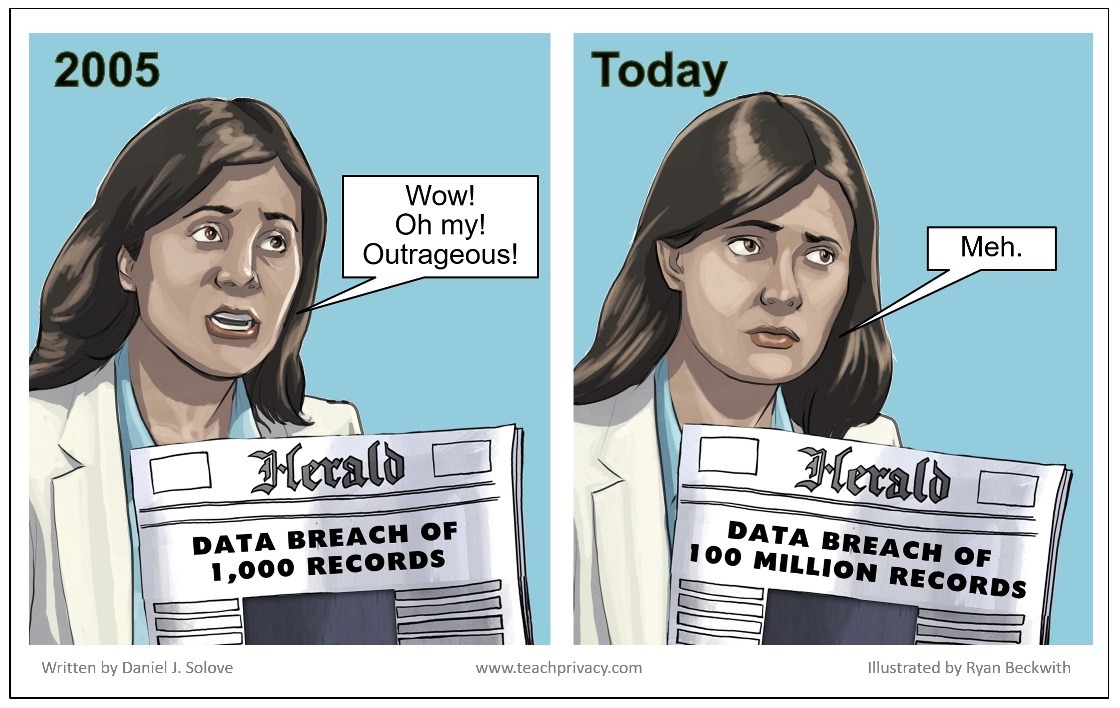
The real question is: why do these numbers still not scare living daylights out of us? Don't worry, it's a common enough condition. Dasera's VP of Products, Thi Thumasathit, broke down the psychological factors that make insider threats seem less threatening.
Is Remote Working Even Remotely Working?

The Coronavirus outbreak threw a giant (and spiky) curveball at us. And we were not prepared for it. Moving into a completely remote working situation opened up a universe of new security challenges. Or a constellation, as per Threatpost.
- And if managing remote employees wasn't enough, a recent Accenture study suggests 40% of security breaches target indirect sources i.e. third parties, partners, contractors. Can't catch a break, can we?
- Video conferencing tool Zoom received a lot of flak for being a breeding ground for privacy violations. Its privacy policy enabled Zoom to collect and store crucial data in the name of “customer content”. Looking at the potential risk, biggies like SpaceX and NASA banned the app, putting the teleconferencing software firm in a "nasty, nasty" spot.
TechRadar offered us some useful tips to deal with both cloud computing and telecommuting. Many tech companies have broadly extended "working from home" till the end of 2020. So, either security teams have things under control, or we're not getting any vacation time this year. (What would we do with it anyways?)
No One is Too Big For Their Breaches
Another season in cybersecurity = many more of the who's who got breached:
- Hawaii Pacific Health (HPH) discovered multiple instances of unauthorized access over five years by an employee of Straub Medical Center in Honolulu. They believe the employee accessed personal health information (PHI) of almost 4,000 patients, but here's the kicker - HPH "believes it was out of curiosity rather than to obtain sensitive information for malicious purposes". That's a bucketful of curiosity, I tell ya.
- Marriott again suffered a data breach. This one affected 5.2 million guests worldwide. It happened through the login credentials of two employees at a franchise property. "Hapless insiders" was a theme this winter.
- If you have a minute, check out this infographic of three very unusual insider breach stories. (Yes, it's a very shameless self-plug.)
Brush Up Your Data Privacy Laws
Everyone's spending time on growth and learning. Leading online learning provider Coursera reported 10 million new users in the past month alone! So here are some useful reading links to keep you on top of your Privacy game.
- 1/3rd of all enterprises spent over $1 million on GDPR compliance alone.
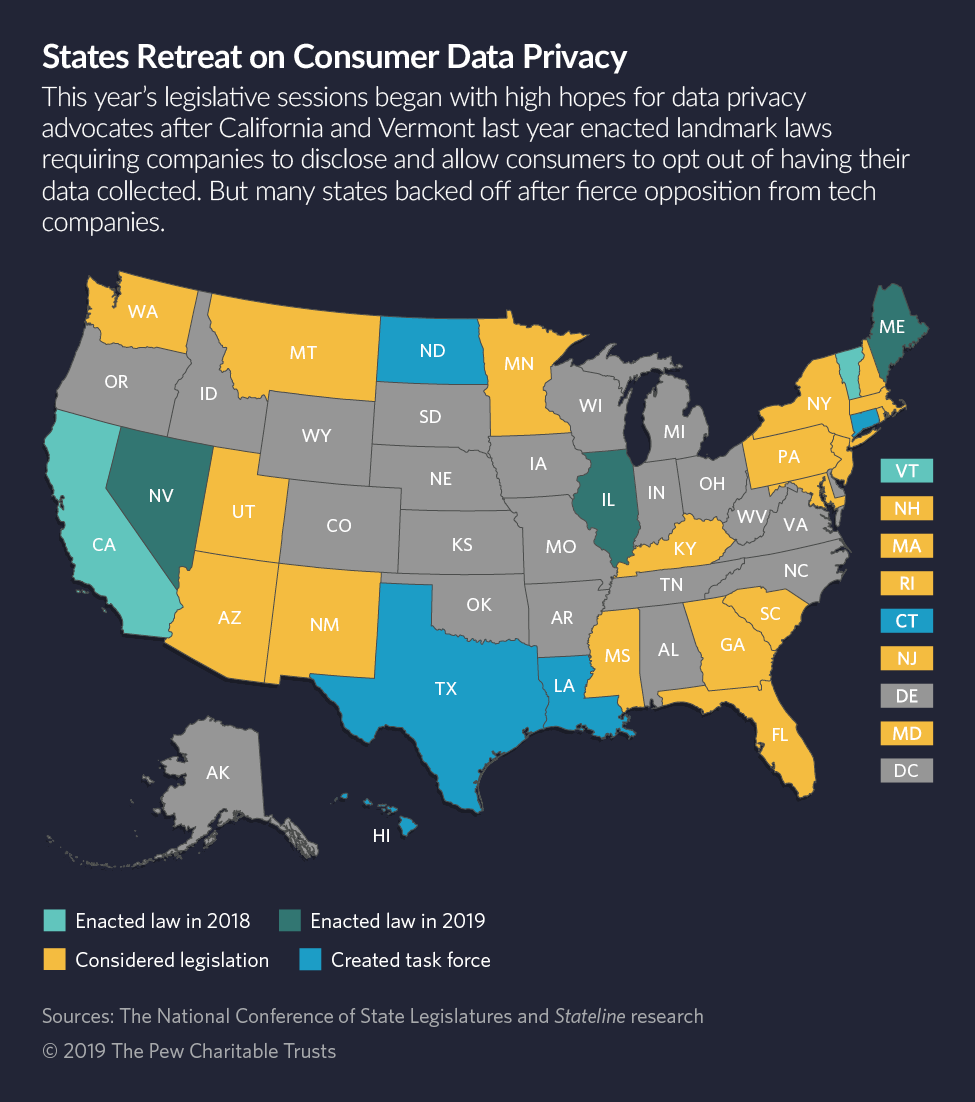
- While many US states are making a beeline to adopt similar regulations, California's CCPA is the trendsetter. And no it's not GDPR with more wine.
- Even with established regulations like HIPAA, there are questions on how recent COVID related waivers affect regulatory requirements in the long run.
Other Useful Stuff
- Some rad Cybersecurity Podcasts to Listen Now!
- A Brief History of the Data Warehouse
- Five interesting takeaways from RSA 2020. Yes, it happened less than 3 months ago!
- Missing live events? Here's a star-studded webinar from SINET: How BODs are Managing During Uncertain Times
Spare Some Love For Us!
Loving what you read? How about paying it forward by sharing this with a friend?










