(This is a blog series on SQL Queries by the Dasera Engineering team. In this first edition, Dasera co-founder and CTO Noah Johnson discusses an often overlooked cloud data risk: queries executed on cloud data)
Companies are collecting petabytes of consumer data. This data is extremely valuable: it generates insights, informs business decisions, improves efficiency, and creates competitive advantage.
Extracting value from the data requires giving access to data analysts, so it’s no surprise that companies are expanding internal data access. Historically, access was given only to a small number of trusted employees. Today, a typical company has thousands of employees with different roles and varying skill levels accessing sensitive data every day.
As more employees have access to sensitive data, the risk of internal breaches increases. More than 10 billion consumer records have been leaked in the last 10 years, and it’s estimated there will be nearly 5,000 internal breaches this year alone.
How can companies provide flexible data access to employees while protecting against data breaches?
Limitations of Existing Solutions
Most security efforts today are externally focused, designed to keep malicious outsiders out. Very few safeguards are in place for insiders who regularly access sensitive data.
Companies typically manage insider risk through the blunt instrument of access control: a given employee either does or doesn’t have access to data. Security is a binary decision.
Access control restricts who is permitted to access sensitive data, but not how the data can be used. This is analogous to a lock on a front door, which prevents unauthorized people from entering the house but provides no protection once someone is inside.
Beyond access control, companies have little to no visibility into how their employees use sensitive data—much less the ability to prevent internal data breaches.
Protecting Sensitive Data Through Query Inspection
An analyst accesses data by executing a query. Every data warehouse supports a query language called SQL and all data access is performed through SQL queries, even when not apparent to the user (e.g. BI tools and applications).
SQL can express nearly any type of calculation including statistics, aggregations, and temporal analysis. This flexibility is why SQL has become the de-facto standard language for data analytics.
However, this flexibility also allows analysts to create security risks—intentionally or inadvertently. Consider the following two queries running on the same database, one of which is safe and the other risky:
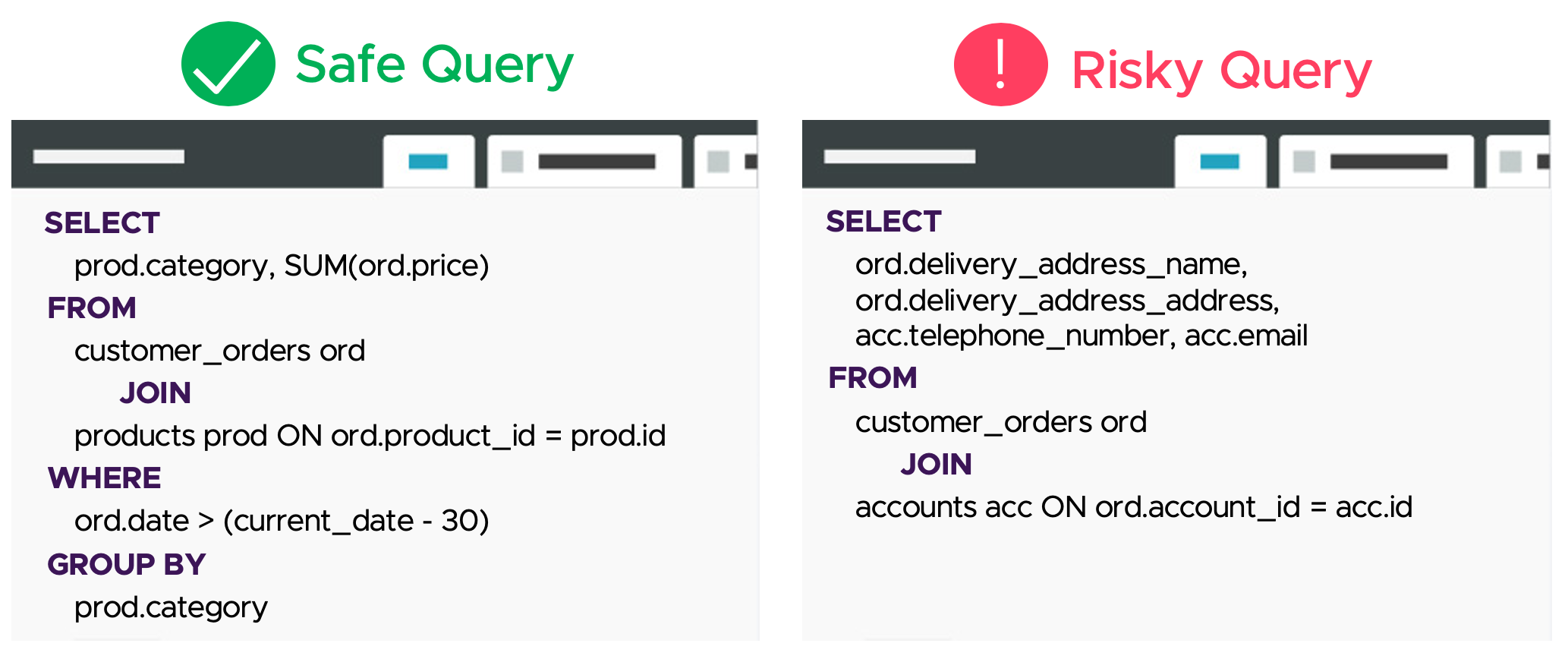
The first query computes the highest performing product category within the last 30 days.
The second query returns all customer orders and accounts. Regardless of whether the intent was malicious or benign (e.g. data exfiltration or an inexperienced analyst) this query poses a security risk because sensitive consumer data is downloaded from the database.
Notice that both queries access consumer data, so a simple access control policy would be unable to distinguish between them.
Risky queries aren’t limited to data exfiltration. For example, a SQL query can create a privacy risk by returning information about a specific individual such as a celebrity or ex-boyfriend.
At a typical company, tens of thousands of queries are executed each day without any evaluation of their security and privacy risk. If an employee (or attacker who compromises an employee’s account) exfiltrates or misuses data via a SQL query, it’s almost certain that no one would be notified.
Query Inspection
At Dasera we believe query inspection is critical for an effective data protection strategy. Queries capture the intent of the employee interacting with the data; understanding this intent is essential for distinguishing safe and risky access, as illustrated in the example above.
By monitoring the queries that run on sensitive consumer data, companies can ensure the data is used safely, responsibly, and only for its designated purpose. Query inspection also allows security teams to detect and respond to incidents quickly.
Query inspection is complementary to access control measures. Returning to the lock analogy, query inspection is analogous to adding a security camera in every room of the house and having a security guard monitor the camera feed.
Next Steps
With increasing collection and use of consumer data comes greater risk. CISOs, CIOs, and security teams must adopt new measures to monitor and control how insiders interact with sensitive data.
In this blog we described how queries can pose a security risk, and why inspection of queries is critical for ensuring safe internal use of consumer data.
In a future blog, we’ll summarize techniques for automated query inspection and discuss how analysis of query logs can be used to detect and remediate data breaches in near real time.
You can subscribe to our blog using the link below.