
As a data and security professional, you were probably affected by the latest zero-day exploit (CVE-2021-44228) targeting the Apache Log4j logging library (Log4Shell).
This logging library is commonly used by enterprise apps and cloud services, with many enterprise deployments supporting private apps. Apache has since released a security update and provided recommended configurations for earlier versions that mitigates the vulnerability's impact. However, we strongly encourage all IT admins to update their software immediately if you haven't already done so.
Update on December 14, 2021: A second Log4j vulnerability was just discovered, and a patch was released already.
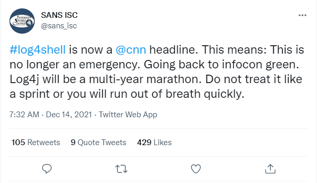 According to SANS ISC, Log4j is here to stay. Meaning it will be a multi-year marathon. So don’t treat it like a sprint or you will burn out quickly.
According to SANS ISC, Log4j is here to stay. Meaning it will be a multi-year marathon. So don’t treat it like a sprint or you will burn out quickly.
Here's a quick cheat sheet list of links to help you in your continued endeavors.
- Log4j (CVE-2021-44228) RCE Vulnerability Explained - Hear from Marcus Hutchins from MalwareTechBlog on the severity and potential impact of Log4j.
- CISA Resources - Log4j Vulnerability Guidance
Visit the Apache Log4j Summary & Resouces
OR
GitHub CISA Log4j (CVE-2021-44228) Vulnerability Guidance - Center for Internet Security - Response recommendations
Visit the CIS Response Resources - SANS Recorded Webinar - What do you need to know about the Log4j (Log4Shell) vulnerability.
- SANS Details - The SANS Interest Storm Center guidance for defending against Log4Shell vulnerability.
- Swiss Government Computer Emergency Response Team - Details and recommendations
- BlueTeam CheatSheet Log4Shell from GitHub
Go to GitHub
And here is what some of our technology partners are suggesting:
1. LogRhythm's blog on the vulnerability
2. Splunk's blog updates for Log4j
3. Microsoft's blog on all things Log4j
4. Snowflake was not impacted by by the vulnerability
5. Google Cloud Armor WAF rule to help mitigate Apache Log4j vulnerability and it's Log4j advisory page









